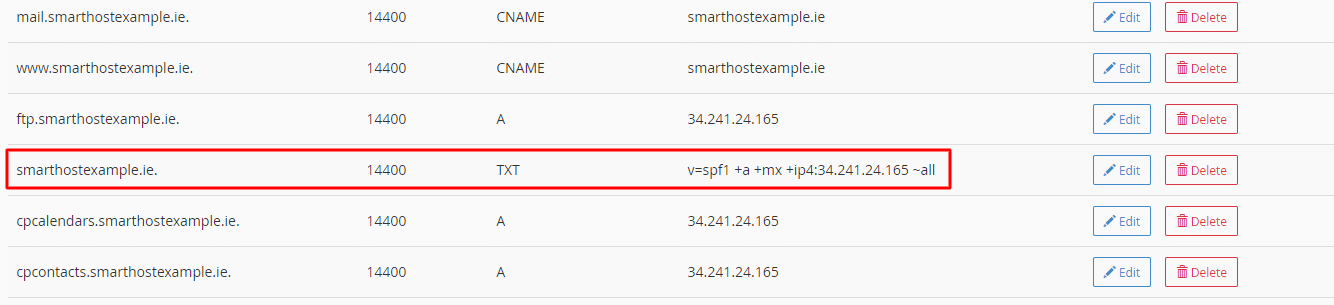
A DNS TXT record called an SPF (Sender Policy Framework) record authorises which mail servers can send email on behalf of your domain. SPF records are an essential tool for preventing email spoofing and phishing attacks. They help ensure that emails sent from your domain pass through spam filters and reach the intended recipients without issues.
The SPF record syntax consists of different mechanisms to specify authorised IP addresses, third-party mail servers, and rules for handling emails that fail SPF checks. For example, an SPF TXT record might look like this:
v=spf1 ip4:192.0.2.0/24 a:mail.example.com -all
In this example record, v=spf1 specifies the SPF version, ip4:192.0.2.0/24 and a:mail.example.com are the authorised IP addresses and domains, while -all indicates that emails from all other servers should be rejected.
- 1
Preventing Email Spoofing: SPF records validate the sender’s identity by checking the sender’s IP address against the authorised addresses in your domain’s DNS records.
- 2
Enhancing Email Deliverability: When you have a valid SPF record, spam filters are less likely to reject emails from your domain.
- 3
Improving Domain Reputation: A proper SPF record improves your domain’s reputation by confirming that you are a legit sender.

SPF records play a vital role in email security by authorising specific mail servers to send mail on behalf of a domain, but they don’t offer a standalone solution. A comprehensive email authentication strategy should also include other technologies like DKIM (DomainKeys Identified Mail) and DMARC (Domain-based Message Authentication, Reporting, and Conformance). Below, we dive deeper into how SPF fits into a larger authentication framework, and why employing multiple layers of security is crucial for optimal email deliverability and domain reputation.<
SPF: The First Line of Defense
SPF records act as the first checkpoint in the email validation system. By checking the sender’s IP address against the SPF record, the recipient mail server can quickly determine if an incoming email is from an authorised source. However, SPF only validates the ‘Return-Path’ domain, not the ‘From’ address displayed to the end user, leaving some loopholes for potential abuse.
DKIM: Digital Signatures for Email Integrity
DKIM serves as a complementary technology to SPF by adding an encrypted signature to the email header. This signature ensures the email content remains untampered with during transit. Unlike SPF, DKIM verifies the ‘From’ address, which is what the end-user sees, offering another layer of trust and authenticity. Implementing both SPF and DKIM provides dual verification, making it more difficult for attackers to spoof your domain.
DMARC: The Policy Enforcer
DMARC ties SPF and DKIM together by setting a policy for what should happen if an email fails either of these checks. It allows domain administrators to specify actions such as ‘report,’ ‘quarantine,’ or ‘reject’ for non-compliant emails. DMARC also enables domain owners to receive reports on email activity, providing valuable insights into potential vulnerabilities or attacks.
Additional Security Measures
- Rate Limiting: To counteract brute-force attacks, implement a rate-limiting mechanism on your mail server.
- Two-Factor Authentication (2FA): Enable 2FA for email accounts to add an extra layer of security.
- TLS Encryption: Use Transport Layer Security (TLS) to encrypt the emails during transit between mail servers.
Regular Monitoring and Updating
Security is an ongoing process. Regularly test your SPF, DKIM, and DMARC configurations to ensure they are working as intended. Use tools like SPF record checkers, DKIM validators, and DMARC reporting services to audit your setup.
Third-Party Email Services
Ensure you include the servers of your third-party email service providers in your SPF records and confirm that they support DKIM and DMARC. Most reputable email services offer easy ways to implement these technologies.
A Holistic Approach
A truly secure email environment requires a holistic approach. SPF records are a significant first step, but they should be part of a multi-layered security strategy that includes DKIM, DMARC, and other security best practices. By implementing a comprehensive eail authentication system, you maximise the chances of your emails reaching their intended recipients while minimising the risks of email spoofing and phishing attacks. This not only enhances email deliverability but also contributes to building a robust domain reputation.
For those using cPanel and WHM, adding a new SPF record is a straightforward process:
- 1
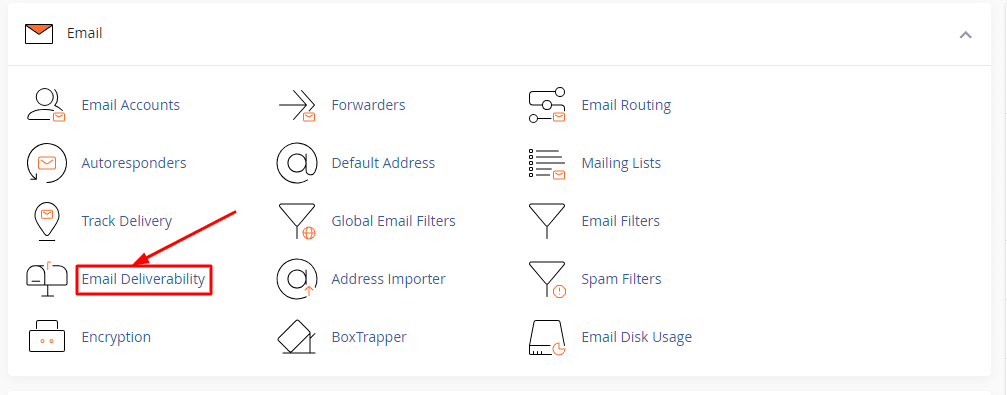
Log in to cPanel: Open your domain account and navigate to the “Email” section.
- 2
Access SPF Manager: Click on “Email Deliverability”.
- 3
Create Your SPF Record: If you don’t have an SPF record yet, cPanel will provide a default one. You can modify it according to your needs.
- 4
Edit Existing SPF Record: If you already have an SPF record, you can edit it by updating the list of authorised IP addresses or adding third-party servers.
- 5
Save and Test: Once satisfied, save your changes and validate the new SPF record using an SPF record checker.
Additional Considerations
- If you are using a third-party DNS provider or email service provider, you may need to add or modify your SPF record manually.
- Regularly test your SPF record to ensure it’s working as expected. Tools like SPF record checker can help you with this.
More Information
Understanding SPF Record Syntax
Mastering the syntax of an SPF record is crucial for setting up an effective authentication system. The syntax can seem daunting at first, but once you break it down into its individual components, it becomes easier to comprehend. By understanding the syntax, you can specify which servers have authorisation to send email on behalf of your domain, thus enhancing your domain’s reputation and email deliverability.
Basic Components of an SPF Record
An SPF record is a type of DNS TXT record and typically consists of:
- SPF Version: Denoted by v=spf1, this indicates the SPF version being used.
- Mechanisms: These define the rules for which IP addresses or domains are authorised to send mail. Common mechanisms include ip4, ip6, a, mx, etc.
- Modifiers: These are optional and provide additional information. The most commonly used modifier is redirect.
Here’s an example SPF record for better clarity:
v=spf1 ip4:192.0.2.0/24 a:mail.example.com -all
- v=spf1: Specifies the SPF version.
- ip4:192.0.2.0/24: Authorises the IP address range 192.0.2.0 to 192.0.2.255.
- a:mail.example.com: Authorises the mail server of mail.example.com.
- -all: Specifies that no other servers are allowed to send mail.
Types of Mechanisms
- IP Mechanisms (ip4 and ip6): Allow you to specify authorised IP addresses or ranges. (Example: ip4:192.0.2.0/24 or ip6:2001:db8::/32)
- Domain Mechanisms (a and mx): Allow authorisation based on domain names and their corresponding MX records. (Example: a:example.com or mx:mail.example.com)
- Include Mechanism (include): Useful when using third-party servers, like email service providers. (Example: include:spf.thirdparty.com)
- Exists Mechanism (exists): Used for complex setups and not commonly used. (Example: exists:config.example.com)
Qualifiers
- + for Pass: This is the default qualifier. If you specify +ip4:192.0.2.0/24, it means that the specified IP addresses are allowed to send email.
- – for Fail (Hard Fail): Indicates that the mail should be rejected if it fails SPF checks.
- ~ for Soft Fail: Emails will still be accepted but marked.
- ? for Neutral: This means that the server neither passes nor fails the SPF check.
Example Records with Multiple Domains
If you manage multiple domains, you can combine SPF records as follows:
v=spf1 include:example1.com include:example2.com -all
This tells spam filters to allow mail servers from both example1.com and example2.com while rejecting all others.
SPF Version
It’s important to note that as of now, v=spf1 is the only SPF version in use. If new versions come out in the future, this part of the record will show which SPF specification version you’re using.
Limitations and Best Practices
- Keep your SPF record concise; exceeding the DNS lookup limit could result in SPF failure.
- Make sure to update the SPF record when changing mail servers or IP addresses to avoid email deliverability issues.
Understanding the syntax of an SPF record is the first step toward optimising your email validation system. By specifying the authorised senders correctly, you not only prevent spoofing but also improve your domain’s chances of passing through spam filters effectively.
How SPF Records Work
Sender Policy Framework (SPF) records serve as a crucial component in the authentication process. While they might seem complex at first, understanding how SPF records function can provide you with invaluable insights into securing your domain’s email communication. In this section, we’ll break down the mechanics of SPF records, how they interact with receiving email servers, and why they are integral to preventing spoofing and improving email deliverability.
SPF Record Lookup: The Initial Step
When an email is sent from your domain to a recipient, the receiving email server performs an SPF record lookup. This process involves querying the DNS (Domain Name System) for the SPF record associated with the domain in the email’s ‘Return-Path’. The server then retrieves the SPF record, which is a TXT record in the DNS, to proceed with the validation.
Validation Mechanism: Checking the Sender’s IP Address
The core of the SPF mechanism lies in validating the IP address of the sending email server. The receiving server compares this IP address against the authorised IP addresses specified in your SPF record. If the IP address is listed as an authorised sender, the SPF check passes. Otherwise, it fails.
SPF Qualifiers: Defining Actions
SPF qualifiers like -all, ~all, and ?all indicate what should happen when an SPF check fails, passes, or is inconclusive. For example, -all would suggest that emails from all other servers not listed in the SPF record should be rejected.
- Pass: The email is accepted as it originates from an IP address or domain listed in the SPF record.
- Fail (Hard Fail): The email is outright rejected.
- Soft Fail: The email is marked but still delivered, indicating it failed SPF but is not necessarily malicious.
- Neutral: The SPF check neither passes nor fails, usually resulting in the email being accepted but marked.
Multiple Mechanisms: Adding Complexity
SPF records can have multiple mechanisms to authorise several IP ranges or specific third-party mail servers. For example, if you’re using an external email marketing service, you can include their servers in your SPF record using an include mechanism.
SPF and Email Forwarding
It’s essential to note that SPF can sometimes break email forwarding setups. When a server forwards an email, the receiving server sees the original ‘Return-Path’ but detects the IP address of the forwarding server, which can cause an SPF failure. To resolve this issue, you may need to use specialised SPF mechanisms or settings on the forwarding server.
SPF and Rate Limiting
SPF alone doesn’t regulate the email sending rate from your domain. However, using SPF can boost your domain’s reputation, reducing the likelihood that receiving servers will rate-limit your outgoing emails.
Limitations and SPF Failure
- DNS Lookup Limit: An SPF record should not exceed a DNS lookup limit of 10, as this can lead to SPF failure.
- Inheritance Issues: Using too many include statements can complicate the SPF record and lead to inheritance issues, where the included domains have their own SPF records.
SPF in Conjunction with Other Protocols
SPF works best when used alongside other authentication protocols like DKIM and DMARC. While SPF validates the ‘Return-Path,’ DKIM ensures the integrity of the message, and DMARC provides a policy framework for handling authentication failures.
Understanding how SPF records work is fundamental to leveraging their full potential. They act as the first line of defense in authenticating your domain’s email, playing a crucial role in preventing spoofing and helping your emails avoid spam filters. By configuring your SPF record thoughtfully and monitoring its performance regularly, you can substantially enhance the security and deliverability of your domain’s email communications.
Frequently Asked Questions (FAQ) on SPF Records

Our team can help
Have further questions, or need some advice about hosting solutions for you and your business?
Our team are on hand to assist you and get your business online. Why not give us a call on (01) 901 9700 or send us an email at support@smarthost.ie. We will get back to you as soon as possible.